
Intelligent Access Control with Advanced Alerts
Monitoring access in real time
Access control is crucial for protecting businesses, organizations, and properties. An intelligent access control system must be able to monitor access in real-time, identify suspicious activities, and send immediate alerts.
Advanced alerts with customizable filters are the ideal solution for effective and intelligent access control. They can be configured with customized access thresholds based on date, time, user, and access point, ensuring the security of monitored facilities.
Cos’è un avviso aWhat is an advanced alert with customizable filters?
An advanced alert with customizable filters is a configurable notification system that sends alerts when it detects suspicious access activity. It can be set with customized access thresholds for:
- Date and time
- User
- Access point
When someone accesses by surpassing one of these thresholds, the system sends an instant notification to administrators allowing them to evaluate the situation and intervene.
How does an advanced alert work?
An advanced alert works by constantly monitoring access activities. When it detects access that surpasses one of the pre-set thresholds, it immediately sends a notification via:
Administrators can thus be alerted in real-time of potentially suspicious or dangerous access and evaluate whether they are authorized or intervention is necessary.
The exact functioning depends on the access control system and the supported notification options, but the basic steps are:
- Configure customized access thresholds for date, time, user, and access point
- Set notification channels to use: email, API, SMS, messaging apps
- Monitor the accesses detected by the access control system
- When a threshold is surpassed, send a notification to administrators via selected channels
- Administrators evaluate the notification and intervene if necessary
Why use advanced alerts?
Advanced alerts are an advantageous option for access control. In particular, they offer real-time access monitoring, allowing the system to immediately identify when a threshold is surpassed.
Administrators receive instant notifications of potentially suspicious or unauthorized access, and thresholds can be customized to meet the specific needs of the monitored organization.
Think for example of the management of a venue and the need to keep track of the maximum capacity of people inside.

In this way, alerts allow for quickly identifying suspicious access and offer greater peace of mind, as the system constantly monitors access and alerts in case of anomalous activity.
Finally, effective access control reduces the risk of unauthorized access, theft, and other illicit activities, contributing to protecting the structure.
Visit us at the Sicurezza 2023 trade fair!
How to implement advanced alerts
If you are looking for a complete and customizable access control system, advanced alerts with customizable filters may be the right solution for you.
Starting today through the new “Limit Alert” feature, you have the possibility to set the number of consecutive times a user can access the access point.

Have you already purchased a LabKey?
Don’t worry! The system update has already been made, from the Manage panel you can request the activation of new Alerts, such as the pre-existing “Virtual Room” and “Limit Alerts”.
In fact, whether it is within a company, a gym, a parking area, or whatever, it is always a positive aspect to be able to know in real-time and in total safety, the number of people inside the “room” (which could be your office or the parking of your hotel) and the number of entries that the member you gave access to has made.
By setting the maximum number of consecutive entries within the manage panel, you can receive an alert if someone tries to access more than once!
HOW TO SET UP THE ALERT?
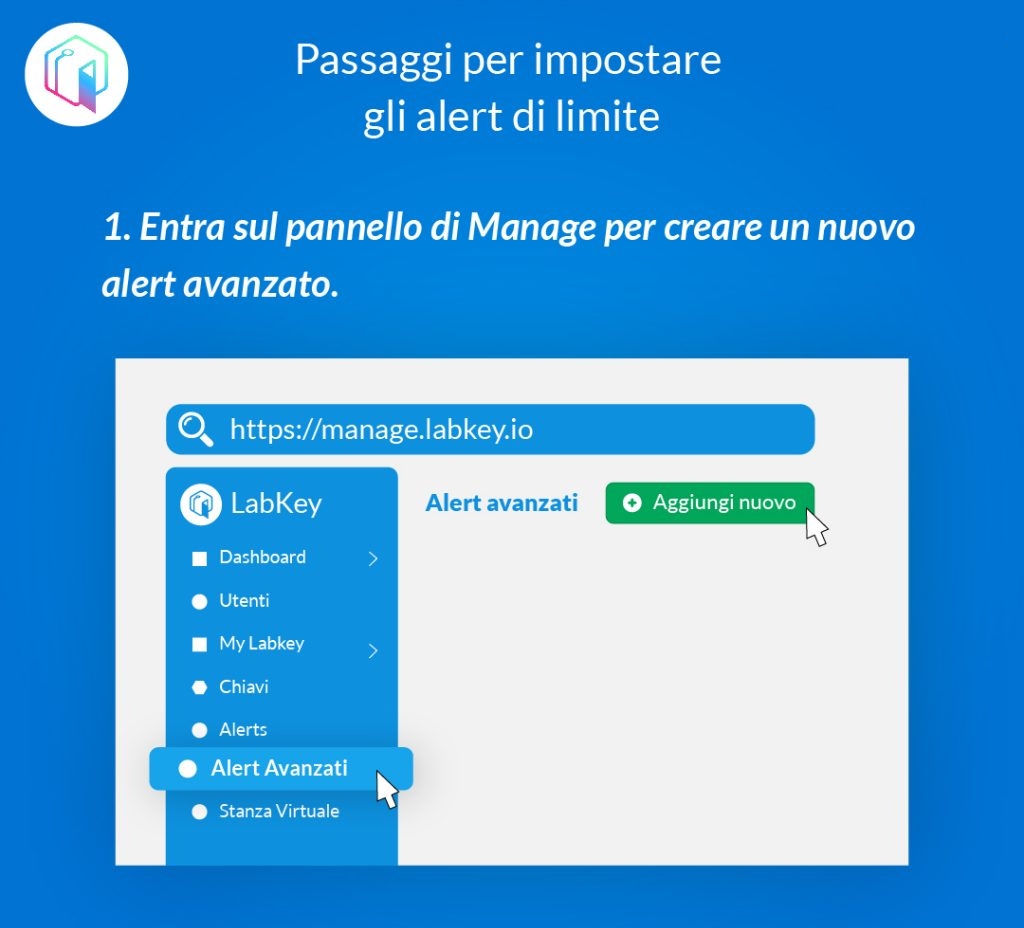
First, enter the manage panel to create an advanced alert.
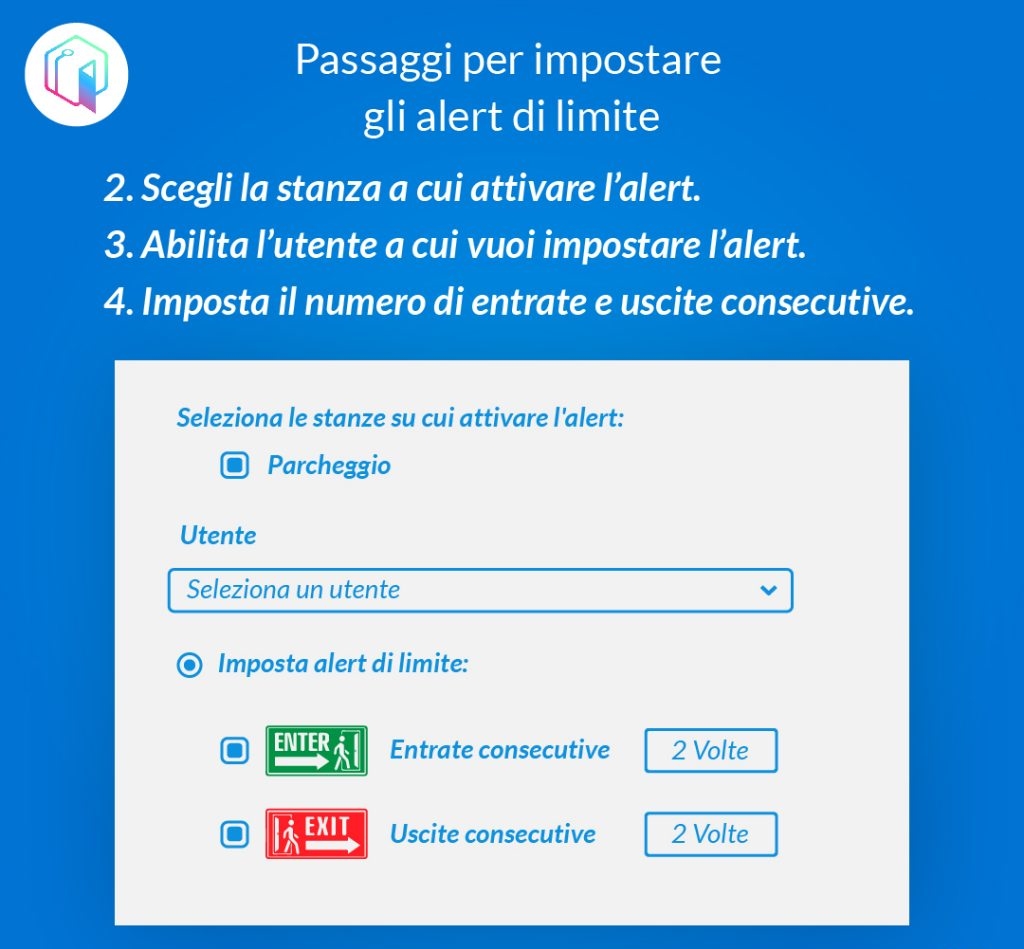
The second step is to choose the virtual room to which you want to activate the limit alert. You can then enable the user you want to set the alert for and finally choose the number of consecutive entries and exits.
ONLY TWO STEPS LEFT!
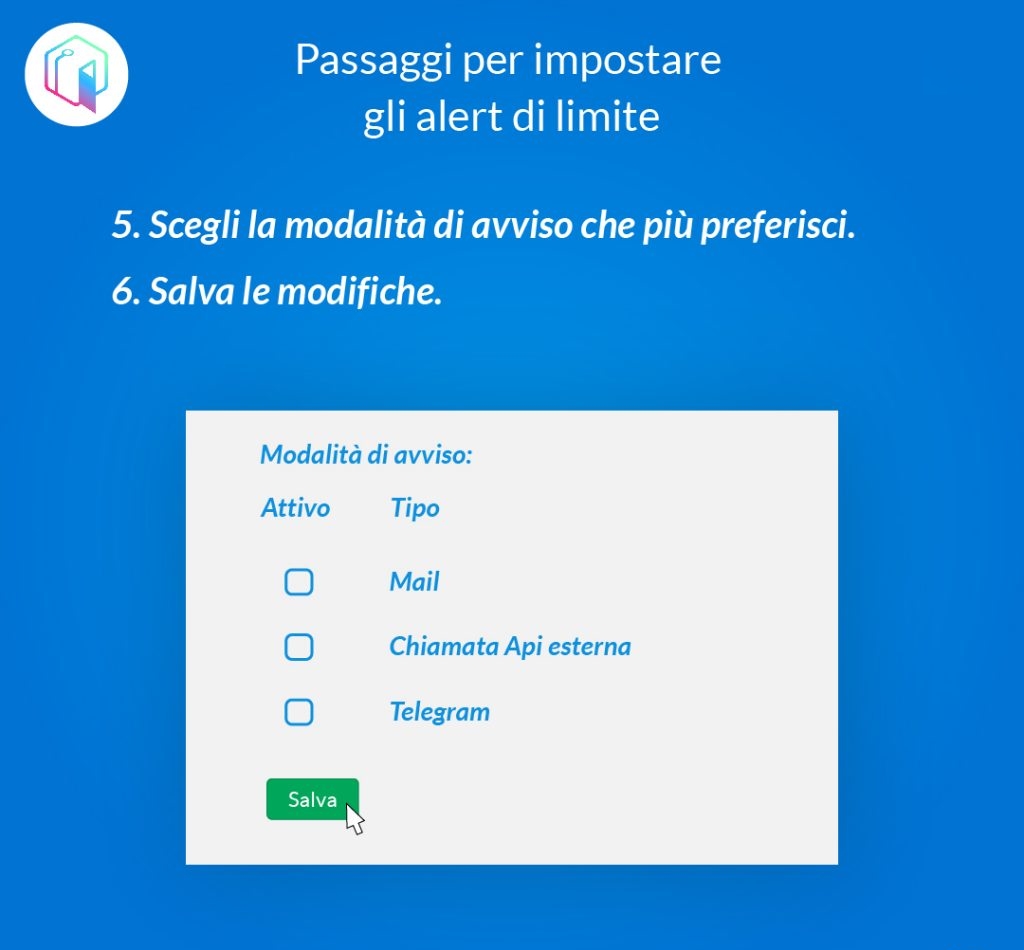
Choose the notification mode you prefer among email, external API call, or Telegram and save your changes!
WHAT CAN YOU DO NOW?
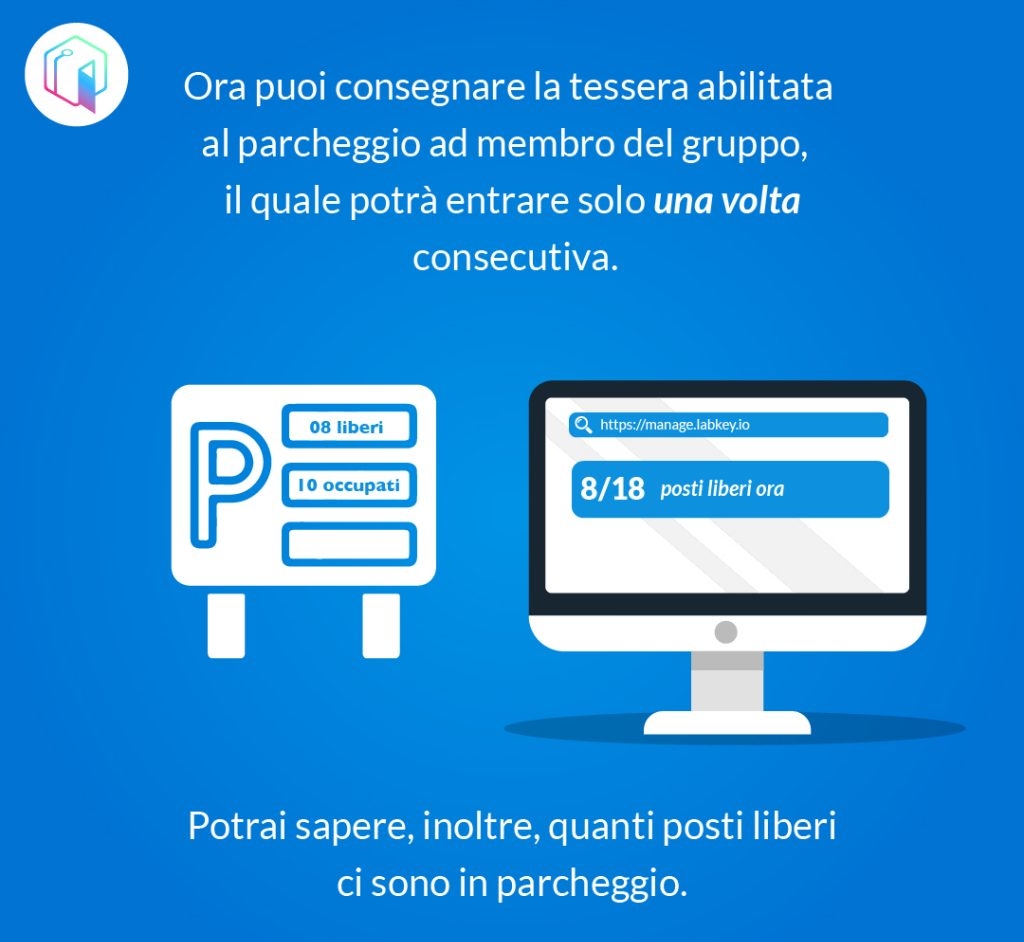
Now that you have enabled your card – for example, for parking – to the desired group member, the latter will be able to access the allowed access point only once consecutively! This will allow you to know how many free spots you have available in your parking lot!
Stay up to date with LabKey and discover with us all of our installations!
Examples of advanced alert usage
Here are some examples of using advanced alerts for an intelligent access control:
Nighttime access monitoring.
Set a threshold to alert if someone accesses outside of working hours, e.g., after 8 pm. Useful for offices, shops, etc.
Visitor access control.
Configure an alert if the same visitor accesses more than 2-3 times in a day or more than 10-15 times in a month. Allows for monitoring potentially suspicious access.
Protection of restricted areas.
Set thresholds to limit access to server rooms, private offices, etc. E.g., alert if more than 5 people access in an hour or if someone accesses after closing time.
Badge usage control.
Monitor the maximum number of badge accesses to identify potential clones or stolen/lost badges used improperly. E.g., alert if a badge accesses more than 10-15 times in a day.
Parking intrusion detection.
Set an advanced alert to monitor the number of cars in a parking lot and alert if the maximum capacity is reached or exceeded. This can help prevent overcrowding and ensure safety protocols are followed.
Employee access control.
Configure alerts for specific employees, such as executives or IT personnel, to monitor their access activities and ensure they are not engaging in unauthorized access. For example, set an alert if an employee accesses outside of their regular working hours or accesses a restricted area.
Overall, advanced alerts with customizable filters offer a flexible and effective solution for intelligent access control. By configuring alerts based on specific thresholds, administrators can be alerted in real-time of potentially suspicious or dangerous access, allowing for quick intervention and ensuring the security of monitored facilities.
Fill in the form for more information
access control, advanced security, API integration, customizable alerts, proactive security solutions, real-time alerts, security management, security notifications, system monitoring, unauthorized access
 LabKey Mini
LabKey Mini LabKey Glass
LabKey Glass LabKey Next
LabKey Next LabKey Extreme
LabKey Extreme Wi-Fi & bluetooth connection
Wi-Fi & bluetooth connection Wi-Fi / LAN Connection
Wi-Fi / LAN Connection Wi-Fi / LTE Connection
Wi-Fi / LTE Connection Local Network Connection
Local Network Connection KIT LABKEY ACCESS PRO 8
KIT LABKEY ACCESS PRO 8